Miktysh Blog.
Your go-to source for everything records management, eDRMS, Office 365, TRIM/Content Manager, RecordPoint, AvePoint, and EncompaaS related.
Categories
Topics
5 Security Features in Office 365 that Keeps Your Information Secure
Nov 30, 2018 | Information Governance, Information Management, Office 365

With the Office 365 suite continuing to expand, one of the most common apprehensions organisations have of moving to the cloud is whether their information will be adequately secured. In this article we’ll discuss 5 security features in Office 365 that you need to be aware of to help dispel the myth that having your information in the cloud is at the expense of security.
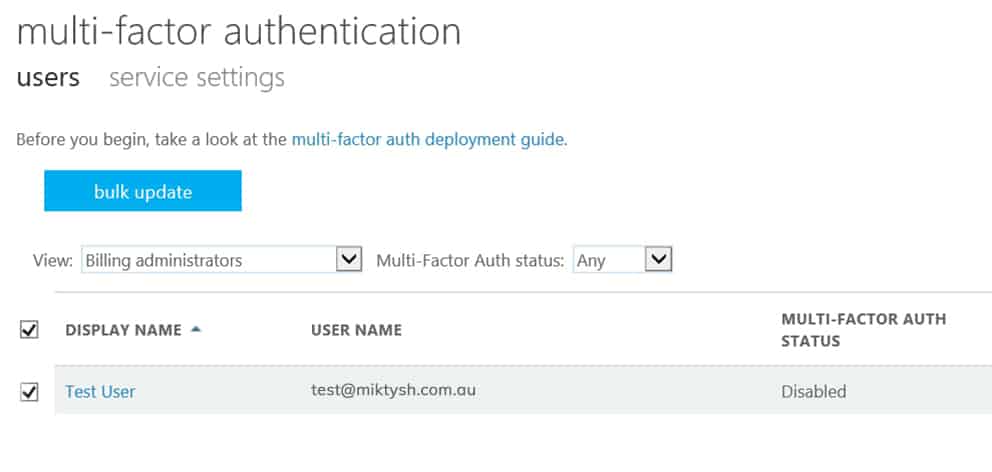
Multi Factor Authentication
Multi factor authentication also referred to as MFA, is an extra layer of protection on top of username and password logins, that is used to prove your identity and prevent unwanted parties from gaining access to your account or network.
In Office 365, you have three different options for verifying your identity. The first is using the Microsoft Authenticator app. Through the app you will be prompted to enter in a one-time-password (OTP), or you will receive a push notification. The second option Office 365 provides is to receive an OTP as a text message, and the third option is to receive a phone call on a number you have registered where you’ll be prompted to press the hash # to verify your identity.
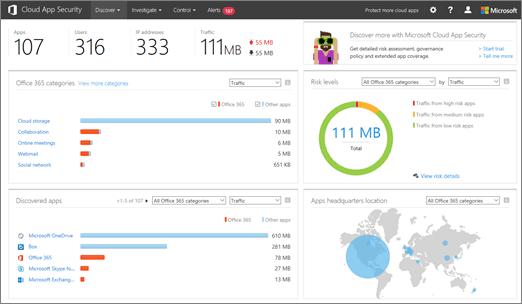
Office 365 Cloud App Security
As aforementioned, security is one of the most common concerns organisations and individuals have when migrating content to the cloud. Microsoft has addressed this concern with the Office 365 cloud app security. Cloud App Security increases the protection of data across Office 365 apps, by allowing your organisation to monitor abnormal activity and act on it.
Alerts can be set up to notify administrators of unusual activity, such as suspicious IP activity, multiple failed logins or downloading a particularly large amount of data. System admins also have the ability to sanction or prohibit user access to specific cloud apps.
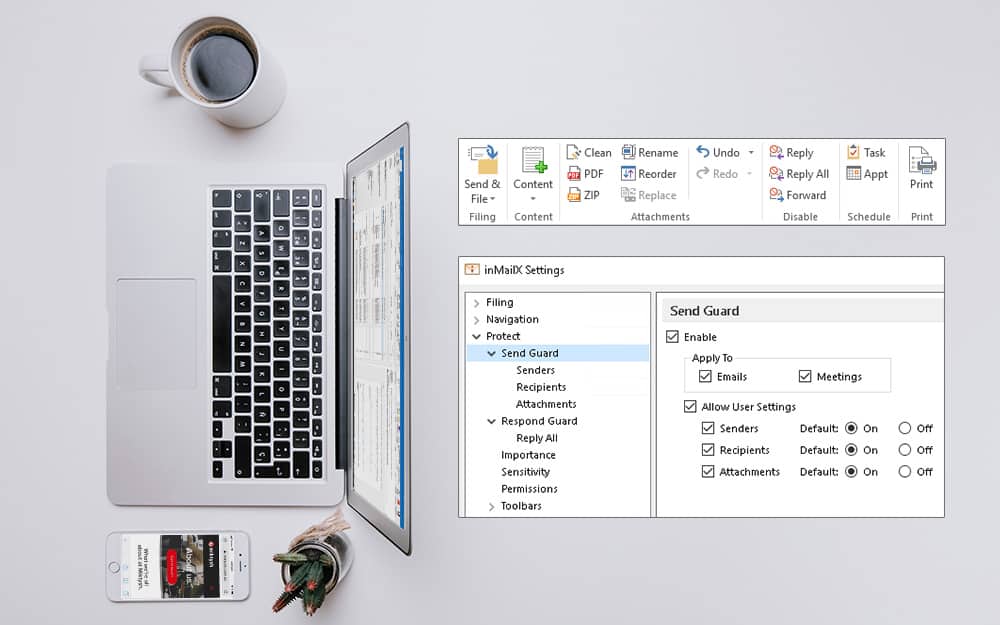
Email Encryption
All businesses deal with sensitive information to varying degrees so it’s imperative when communicating this information internally or externally via email, to ensure this data is properly encrypted. Outlook provides three different encryption options depending on your security requirements. These are; Office Message Encryption (OME), Secure/Multipurpose Internet Mail Extensions (S/MIME) and Information Rights Management (IRM).
OME allows users to send encrypted emails internally or externally, regardless of the email address of the recipient. Microsoft recommends this type of encryption if you’re wanting to communicate sensitive information to people outside of your business.
IRM applies usage restrictions to email messages sent, which prevents these messages from being copied, forwarded or printed by unauthorised people. Microsoft recommends this type of encryption when you want to restrict certain usages in addition to having standard OME encryption.
S/MIME is certificate-based encryption and allows users to both encrypt emails and digitally sign them, in order to validate the identity of the sender. Microsoft recommends using this method of encryption if you are a government agency communicating with other government agencies.

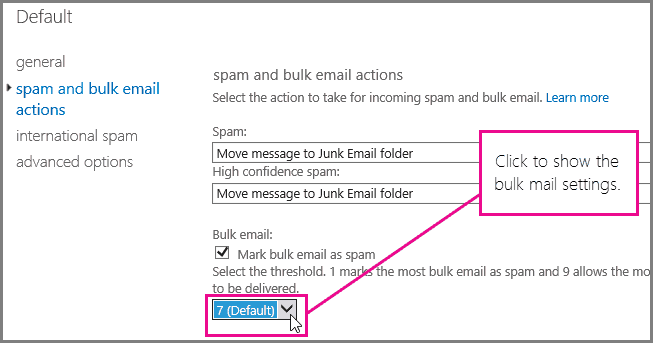
Secure Mail Flow
In addition to email encryption, organisations can protect themselves against malicious viruses and malware transmitted through emails by harnessing the capabilities of Office 365 and Exchange Online Protection.
Connection filtering in Office 365 assesses the trustworthiness of the sender before allowing the email to go through. Administrators have additional functionality to create an ‘allowed’ or safe sender list, or even stipulate to always receive emails from a specific IP address or range.
Spam filtering analyses messages to see if their content is consistent with spam. You can choose what actions take place on messages that Office 365 identifies as spam, as well as choose to filter messages from a particular country or that are written in a particular language. There are also options to have an email notification sent to end-users to notify them when an email sent to them was filtered as spam.
Advanced Threat Protection (ATP) can also be added to your Office 365, which helps further protect your organisation by scanning email attachments and web addresses for malware, as well as having the ability to identify and block malicious files in SharePoint, OneDrive and Microsoft Teams.
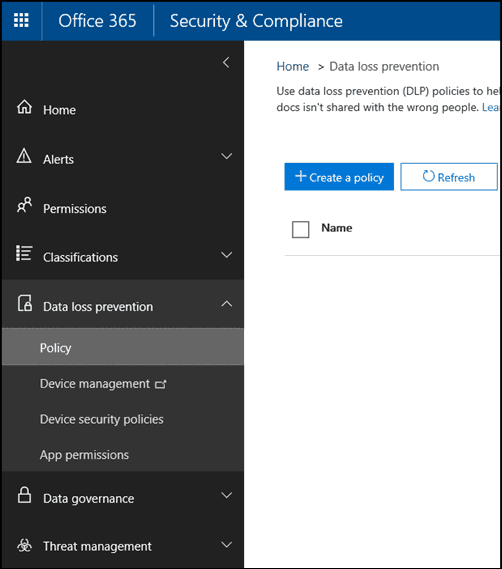
Data Loss Prevention
In addition to data encryption, Office 365 provides functionality to prevent information from being lost in transit, or from being unintentionally disclosed. This can be achieved in Office 365 through the creation of data loss prevention (DLP) policies, which ensure sensitive information is not leaked outside of your organisation. DLP policies go beyond just Microsoft Outlook, and work with repositories such as SharePoint, OneDrive as well as common applications including Word and Excel.
DLP policies do more than just help protect information from being leaked, and also help organisations remain compliant. Microsoft provides ready made templates for this purpose, which are designed to align with most regulatory and compliance requirements.
As the Office 365 suite continues to grow, so does the requirement for added security. Microsoft is meeting this requirement, by continuing to add layers of security that can be customised and configured to best meet the requirements of your organisation. Learning what security features are available in Office 365 should help ease any apprehension organisations may have, of moving to the cloud as technology continues to evolve.
To learn more about SharePoint and Office 365, consider one of the training courses we offer. Or if you’re interested in discussing how Office 365 can be implemented and structured to enhance collaboration and compliance in your business, contact one of our information management experts.

Liza Tinker
Business Consultant
Liza is a SharePoint consultant with over 15 years’ experience in the private and public sector in the use and delivery of SharePoint and other collaboration solutions using Microsoft 365. She is passionate about technology and improving productivity and quality through collaboration and innovation.
Follow us on social
Popular content.

Analytics Driven Information Governance
14.07.2021

The New Normal Requires Zero Trust
27.06.2021
Microsoft 365 Records Management Whitepaper
06.11.2020

Micro Focus Launches Content Manager Select
28.05.2020
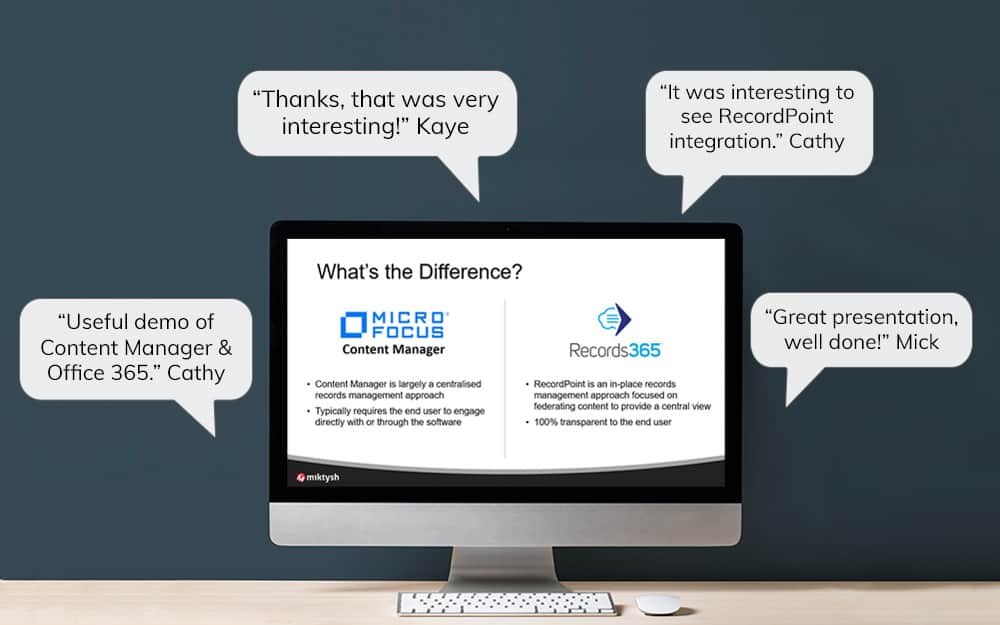
Content Manager SharePoint Integration Demo
20.05.2020

Top 7 Hidden Features in Microsoft Teams
11.02.2020

Integrate Content Manager with SharePoint
15.01.2020

Information Management Strategy Example
06.12.2019
How to Approach a Digital Transformation
13.11.2019

Top 5 Benefits of Migrating to Office 365
10.10.2019
Content Manager 9.4 Web Client
19.09.2019
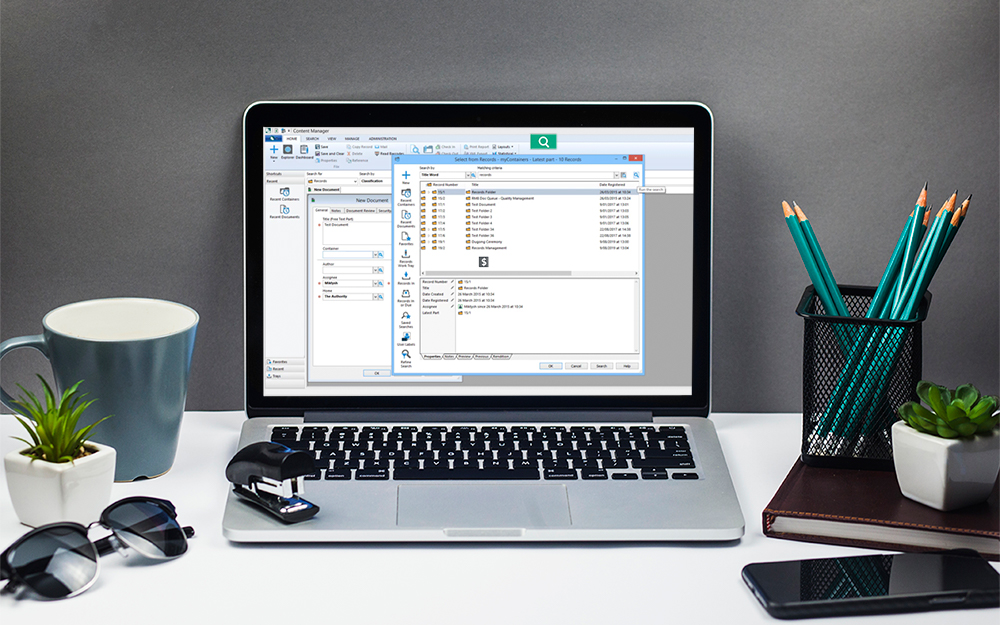
Content Manager 9.4 Sneak Peek – Video Demo
02.09.2019
What Version of SharePoint is on Office 365?
27.06.2019
New SharePoint 2019 Features
08.03.2019

Data Migration Validation Best Practices
08.02.2019

Cloud Governance – RIMPA Queensland Event
27.09.2018
RecordPoint Records365 Demo
09.05.2018

How RecordPoint Enhances Office 365
09.05.2018
6 GDPR Tools to Assist with GDPR Compliance
17.04.2018

Analytics Driven Information Governance
14.07.2021

The New Normal Requires Zero Trust
27.06.2021
Microsoft 365 Records Management Whitepaper
06.11.2020

Micro Focus Launches Content Manager Select
28.05.2020
Content Manager SharePoint Integration Demo
20.05.2020

Top 7 Hidden Features in Microsoft Teams
11.02.2020

Integrate Content Manager with SharePoint
15.01.2020

Information Management Strategy Example
06.12.2019
How to Approach a Digital Transformation
13.11.2019

Top 5 Benefits of Migrating to Office 365
10.10.2019
Content Manager 9.4 Web Client
19.09.2019
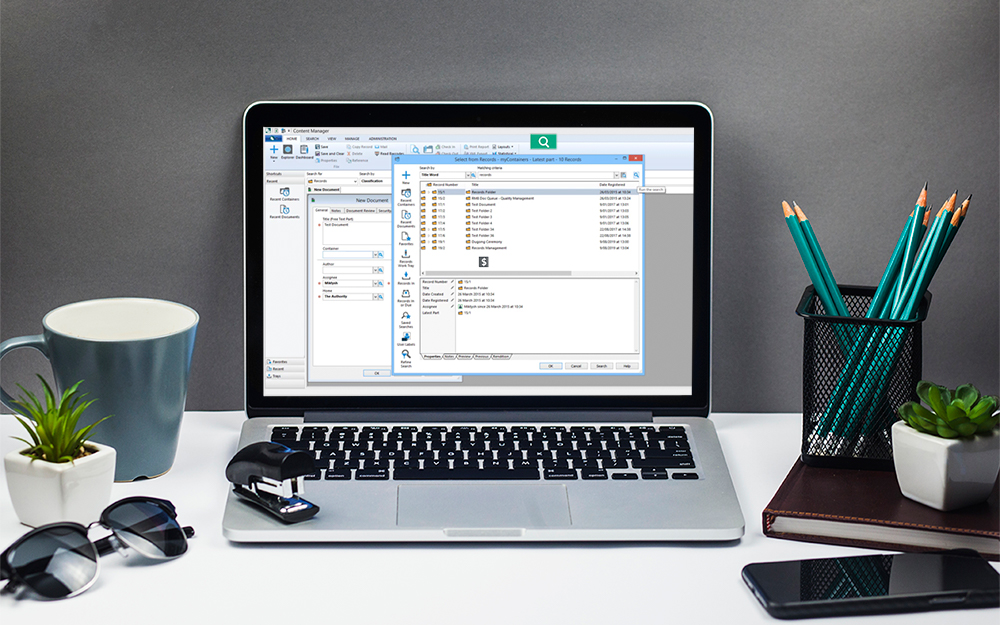
Content Manager 9.4 Sneak Peek – Video Demo
02.09.2019
What Version of SharePoint is on Office 365?
27.06.2019
New SharePoint 2019 Features
08.03.2019

Data Migration Validation Best Practices
08.02.2019

Cloud Governance – RIMPA Queensland Event
27.09.2018
RecordPoint Records365 Demo
09.05.2018

How RecordPoint Enhances Office 365
09.05.2018
6 GDPR Tools to Assist with GDPR Compliance
17.04.2018