Digital Transformation.
Your go-to source for articles and videos on the topic of digital transformation.
Categories
Topics
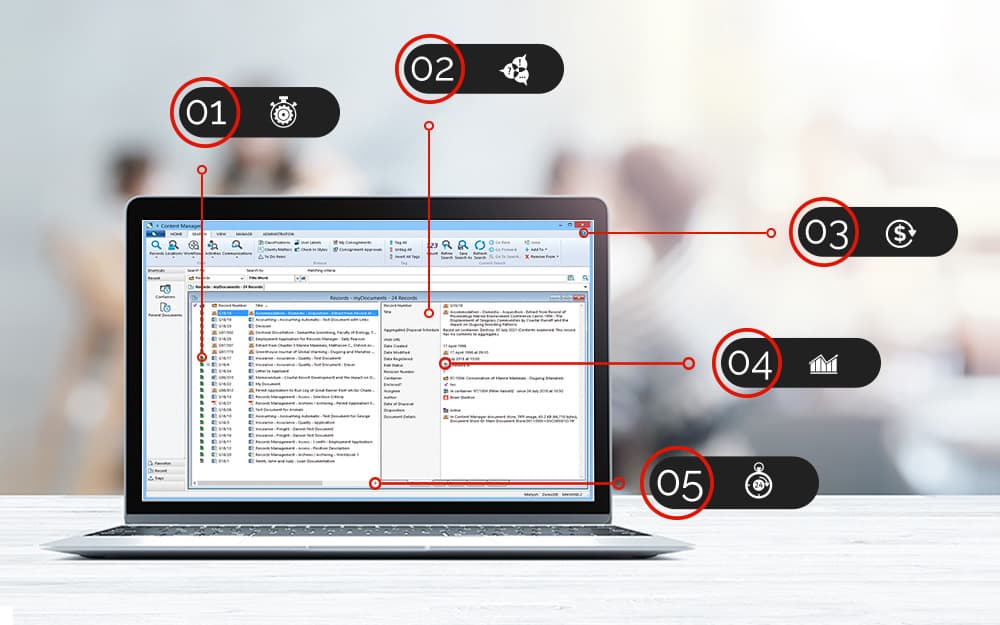
Adding Context to Information for Better Records Management
Oct 22, 2021 | Digital Transformation, Information Governance, Information Management, Office 365
The ‘zero trust’ security emphasizes that enterprises should have a “trusted” internal network and an “untrusted” external network. The adoption of increasing mobile and cloud and the recent pandemic shows that we can no longer have a network perimeter-centric view of security. Instead, we need to securely enable access for the various stakeholders, including employees, partners, contractors, etc., regardless of their location, device, or network. There is no silver bullet in achieving a ‘zero trust’ security architecture. Still, the identity and access management is the core technology that sets the stage for the ‘zero trust’ journey. The ‘people’ become the new perimeter in this journey, with identity-forming the critical component to establishing a secure environment.
In this presentation by Sami Laine from Okta, you will hear about:
· the shifts in the security landscape that paved the way for ‘zero trust’
· how the ‘zero trust’ extended ecosystem will look like today
· building an effective ‘zero trust’ program and architecture for the future.
Popular posts

Analytics Driven Information Governance
14.07.2021

The New Normal Requires Zero Trust
27.06.2021
Microsoft 365 Records Management Whitepaper
06.11.2020

Micro Focus Launches Content Manager Select
28.05.2020
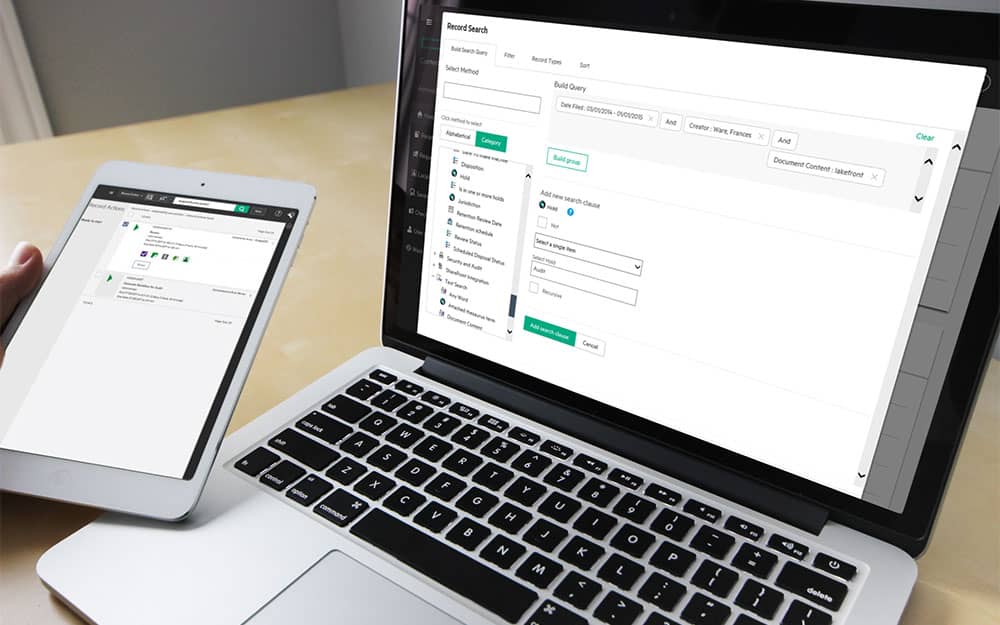
Content Manager SharePoint Integration Demo
20.05.2020

Top 7 Hidden Features in Microsoft Teams
11.02.2020

Integrate Content Manager with SharePoint
15.01.2020

Information Management Strategy Example
06.12.2019
How to Approach a Digital Transformation
13.11.2019

Top 5 Benefits of Migrating to Office 365
10.10.2019
Content Manager 9.4 Web Client
19.09.2019
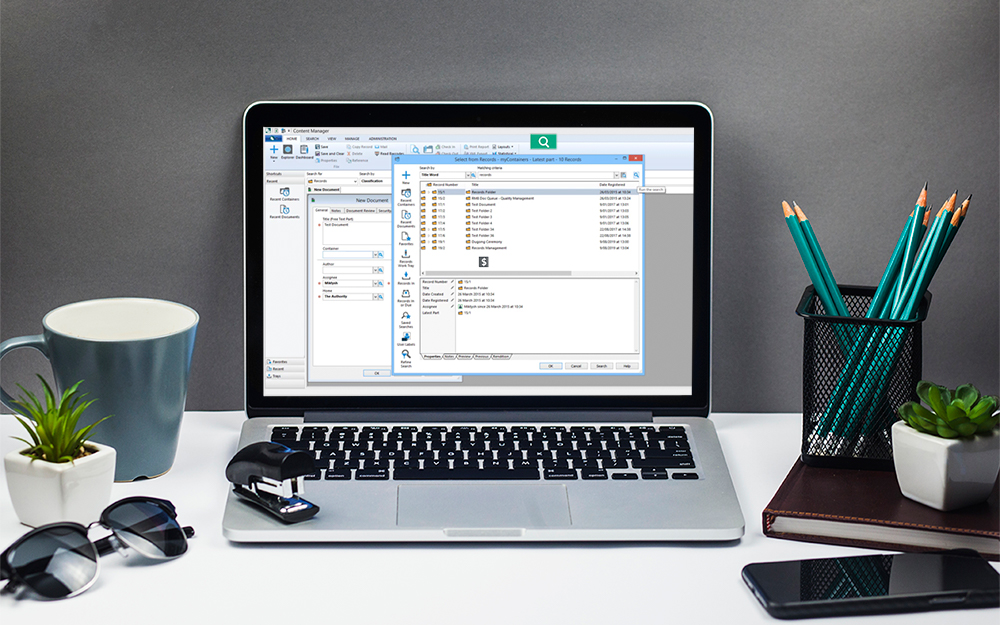
Content Manager 9.4 Sneak Peek – Video Demo
02.09.2019
What Version of SharePoint is on Office 365?
27.06.2019
New SharePoint 2019 Features
08.03.2019

Data Migration Validation Best Practices
08.02.2019

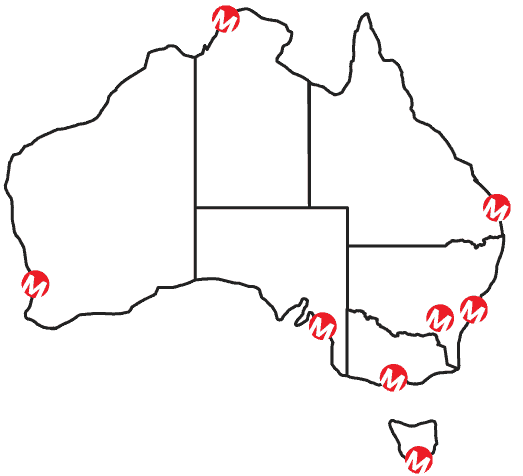
Cloud Governance – RIMPA Queensland Event
27.09.2018
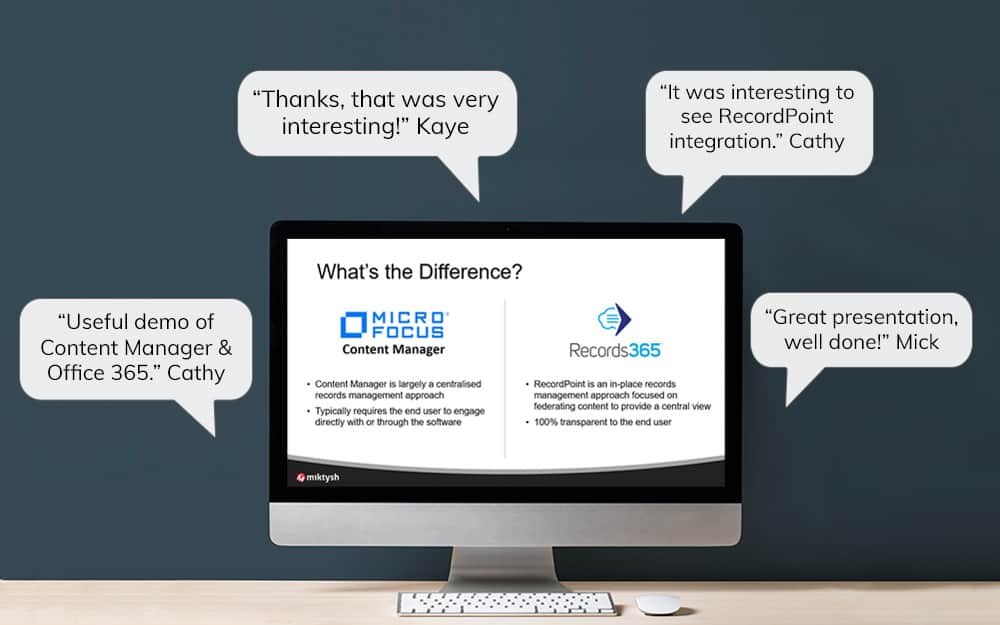
RecordPoint Records365 Demo
09.05.2018

How RecordPoint Enhances Office 365
09.05.2018
6 GDPR Tools to Assist with GDPR Compliance
17.04.2018